Online security is very important for people in the area. Government agencies, independent newspapers and public service providers need it to function. The Threat Analysis Group (TAG) is working around the clock to ensure the safety and security of our users and the platforms that help them access and share important information.
Our longstanding efforts to take action against threat actors in this region are continuing. In the last year, TAG has issued hundreds of government-backed attack warnings to Ukrainian users, warning them that they have been the target of government-backed hacking.
Over the past two weeks, TAG has observed activity from a range of threat actors that we regularly monitor and are well-known to law enforcement, including FancyBear and Ghostwriter. This activity can be classified into espionage and phish campaigns. We are sharing this information to raise awareness among the security community and high risk users.
UkrNet is a Ukrainian media company and has been the target of several large credential phish campaigns. Phishing emails are sent from compromised accounts and include links to attacker controlled websites.
In two recent campaigns, the attackers used a newly created domain, called Blogspot, as the initial landing page, redirecting targets to phish pages. All attacker-controlled domain names have been taken down.
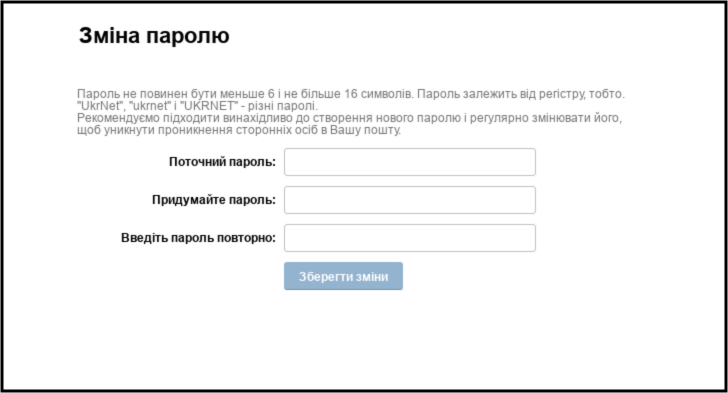
An example of a phish page.
There are examples of credential phish domains observed during these campaigns.
Ghostwriter/UNC1151, a threat actor, has been conducting credential phish campaigns against Polish and Ukrainian government and military organizations. The following providers have been identified by TAG as having campaigns targeting webmail users.
There are examples of credential phish domains observed during these campaigns.
The domains were blocked through a service that identifies unsafe websites across the web and notifies users and website owners of potential harm.
The Chinese threat actor Temp.Hex targeted European entities with lures related to the Ukrainian invasion. There were malicious attachments with file names such as "Situation at the EU borders with Ukraine.ZIP" The zip file contains a basic downloader that can be used to download additional files when executed. To mitigate harm, TAG contacted relevant authorities.
The shift from Southeast Asian targets to European ones has been represented by the targeting of European organizations.
There are attacks on the internet.
The Ministry of Foreign Affairs, Ministry of Internal Affairs, and Liveuamap are just a few of the websites that have seen attempts to hack. We expanded eligibility for Project Shield so that Ukrainian government websites, embassies worldwide and other governments in close proximity to the conflict can stay online, protect themselves and continue to offer their crucial services and ensure access to the information people need.
Project Shield is a tool that allows websites to continue operating and defend against attacks by absorbing bad traffic. Over 150 websites in Ukraine are using the service. We encourage all eligible organizations to register for Project Shield so that our systems can help block these attacks.
We will continue to take action, identify bad actors and share relevant information with others, with the goal of bringing awareness to these issues, protecting users and preventing future attacks. While we are keeping a close eye on activity related to Ukraine and Russia, we are also keeping a close eye on other threat actors around the world to make sure they don't take advantage of everyone's focus on this region.