Ransomware attacks continue to be a problem, but this time it is on the other side. Europol, after a two-year investigation, announced this week that 12 criminals were captured by Europol. They were responsible for ransomware attacks against critical infrastructure around the globe.
Advertisement
Europol claims that the suspects may have attacked more than 1,800 people in 71 countries. This group is well-known for attacking large businesses. They are suspected to be behind the attack on Norsk Hydro, a global aluminum manufacturer based in Norway in 2019. The attack forced Norsk Hydro to cease production in its two factories across two continents. Norsk Hydro was paralysed for nearly a week by the attack, which cost it more than $50million.
Europol seizes more than $52,000 cash and five luxury cars from the suspects. Europol is currently conducting a forensic analysis of the electronic devices of the suspects to identify and secure new leads.
Europol and Eurojust coordinated the international sting, which included eight authorities from eight countries, including the U.S. According to Europol, the sting took place in Ukraine on October 26th and in Switzerland on October 26th.
It is not clear if the suspects have been charged or arrested. Europol has stated that they were targeted.
G/O Media could get a commission Black Friday Deals 2020: What to Expect and What's on Sale Now. Show the suppy chain who is boss
Amazon, Target, Best Buy and other retailers offer holiday shopping tips to help you get started. Black Friday Deals - Shop early
The agency stated that most of these suspects are high-value targets as they are being investigated in multiple high profile cases in different jurisdictions.
Each cybercriminal had a different role in the criminal organization. One of the cybercriminals was responsible for hacking into victims' IT networks. They used various methods, such as brute force attacks and SQL injections.
Advertisement
Once their friends had accessed the victims' IT networks, others got to work. Europol explained that they would then deploy malware such as Trickbot and other tools to keep them under the radar and gain access to more victims' networks.
The criminals would remain undetected in compromised systems for several months probing for further weaknesses in the IT networks, Europol stated. Then, they would move on to monetising their infection by using ransomware.
Advertisement
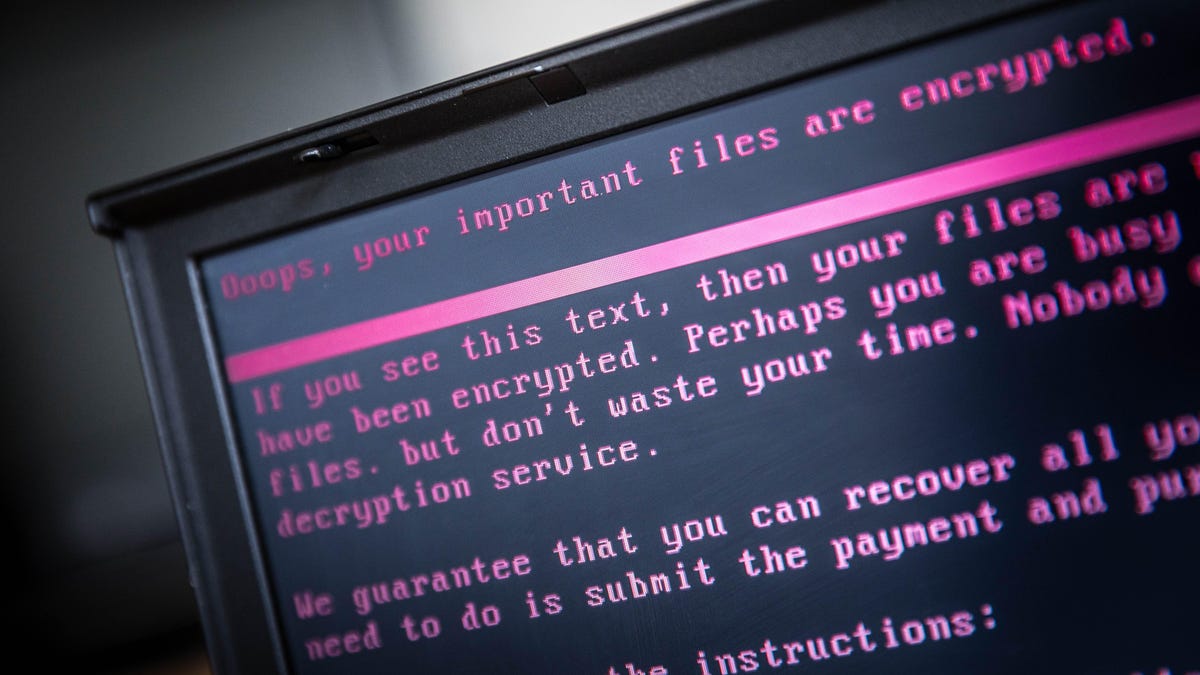
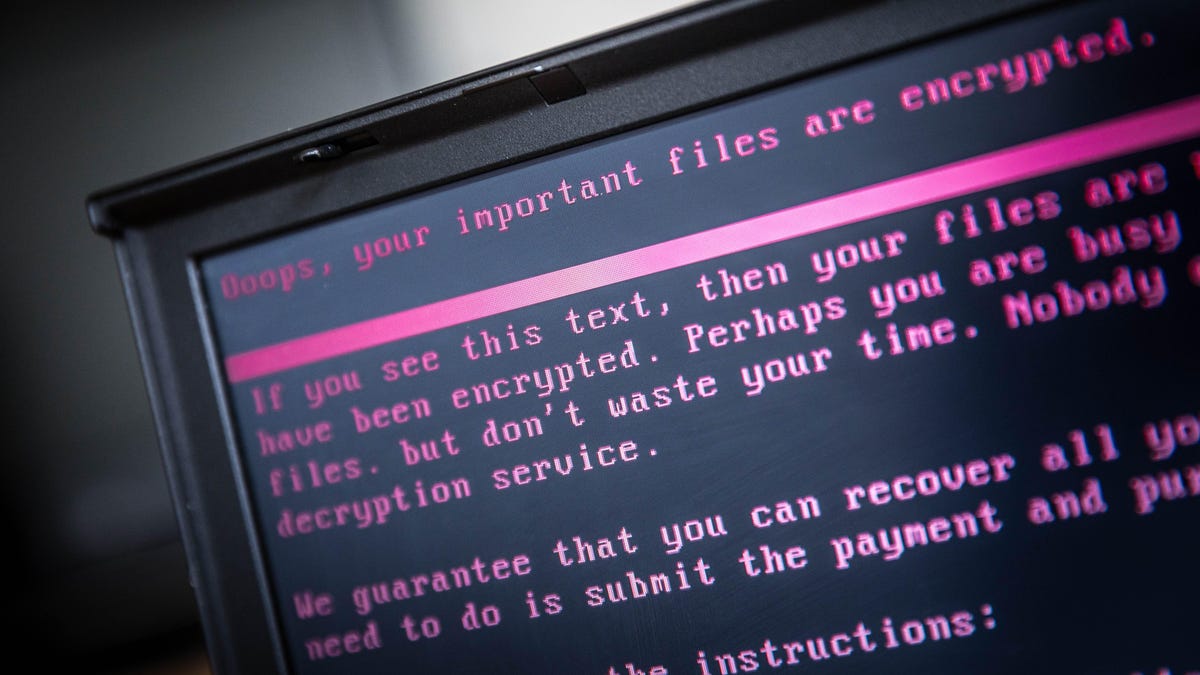
The story takes a twist and turns into one that most of us are familiar with: An attacker encrypted the victim's files, then sent a ransom request for bitcoin payment in return for decryption keys. Some suspects were said to be responsible for laundering the money through the use of mixing services and cashing out.
Europol didn't provide any details about the identities of the victims or the reasons they might have been targeted. Ransomware attacks are also on the rise across the pond. Cybercriminals have launched attacks against large IT corporations and disabled infrastructure.