Two-factor authentication should be used on all accounts that offer it. It is the best way to protect your account. No matter who you are, you want all your accounts to be as safe as possible. It doesn't matter what phone you have, 2FA works on any Android phone. All of this has been said before. However, not all two-factor options are created equal. You have to sacrifice some convenience in order to protect your users. The most secure 2FA methods are often the least convenient. The most secure methods can also be the easiest to use. VPN Deals: A lifetime license is $16, with monthly plans starting at $1. We'll be discussing the pros and cons of each method. It's better to avoid at all cost, but it's better than nothing. Two-factor authentication via SMS
Source: Jeramy Johnson / Android Central
A text message with a 2-factor code and a password is the best way to get an online account. It's also the most insecure. SMS-based 2FA can be very convenient. It is also not very secure. When you sign up for an account, you give your number. If you later enable 2FA, the number will be used to send you a code whenever you need it to verify that you are who you say you are. It is super simple and convenient, which means that many people use it. Many companies also offer it as the only way to get an account. While convenience and ease of use are wonderful, there is nothing special about SMS. Because SMS is an industry standard, even Signal's encrypted and secure messaging app sends plain text SMS messages. SMS was not designed to be secure. Malwarebytes senior malware intelligence analyst Nathan Collier describes SMS as follows: SMS messages can be intercepted while in transit and stored on plain text servers. It is possible to send SMS messages to the wrong number. Even if messages are sent to the correct number, the recipient does not receive notification as to whether or not the message has been read. The problem is even worse: carriers can be tricked into authorizing a SIM card by using another person's phone number. You don't need to convince your carrier to give you access to your bank account, or to order Amazon products using your credit card. All they have to do is convince your carrier that you are you and that you lost your phone. Then, they will need to move your number to the new SIM card they hold. This is also true for email-based authentication. Email is the only way to recover an account. Many banks will send you an email code to allow you to log in using a new device. It's not secure, and everyone in the industry is aware of it. Perhaps it's time to fix how email is used to support this type of thing. This is the best way to use it. Apps for authenticating
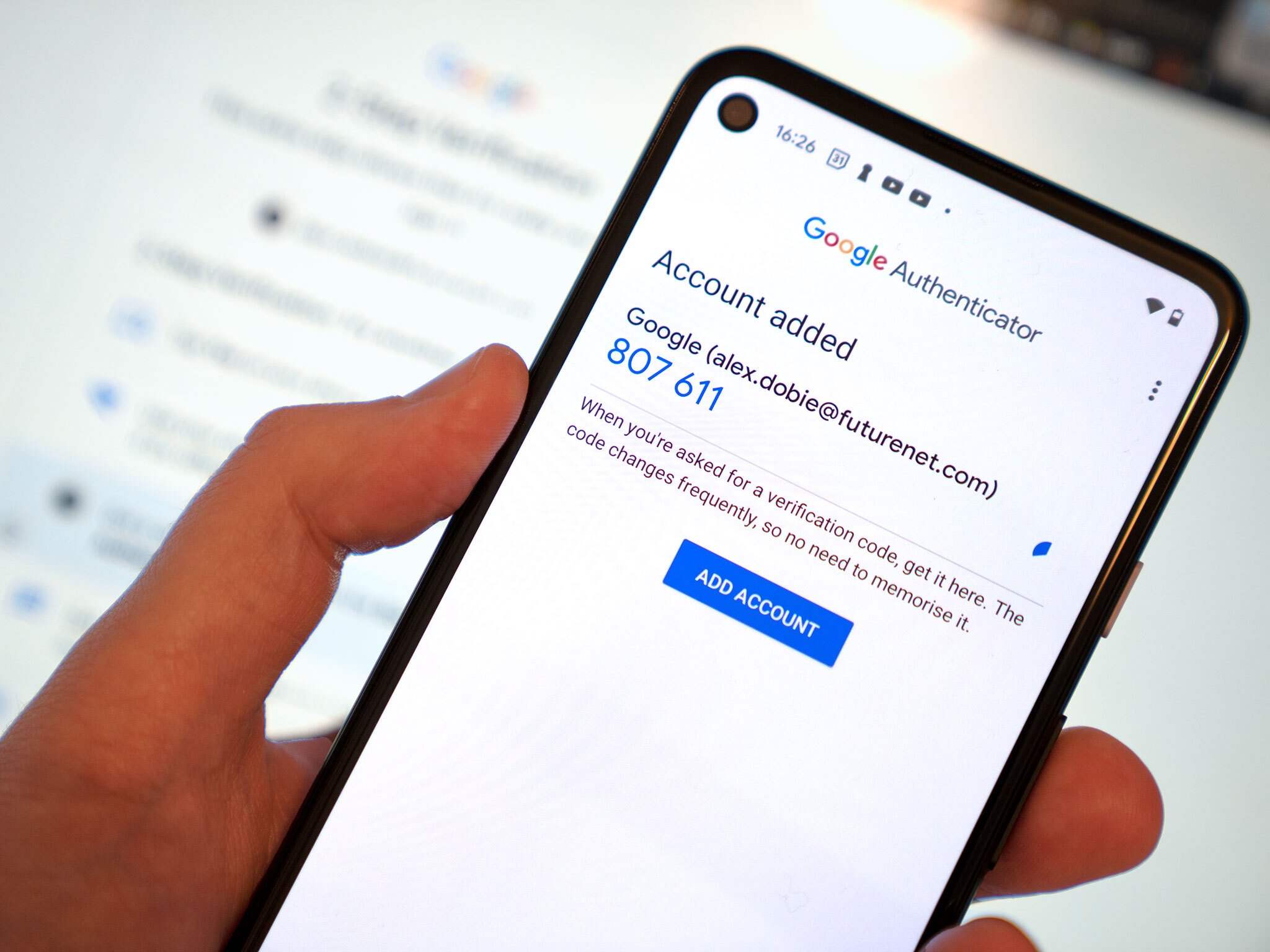
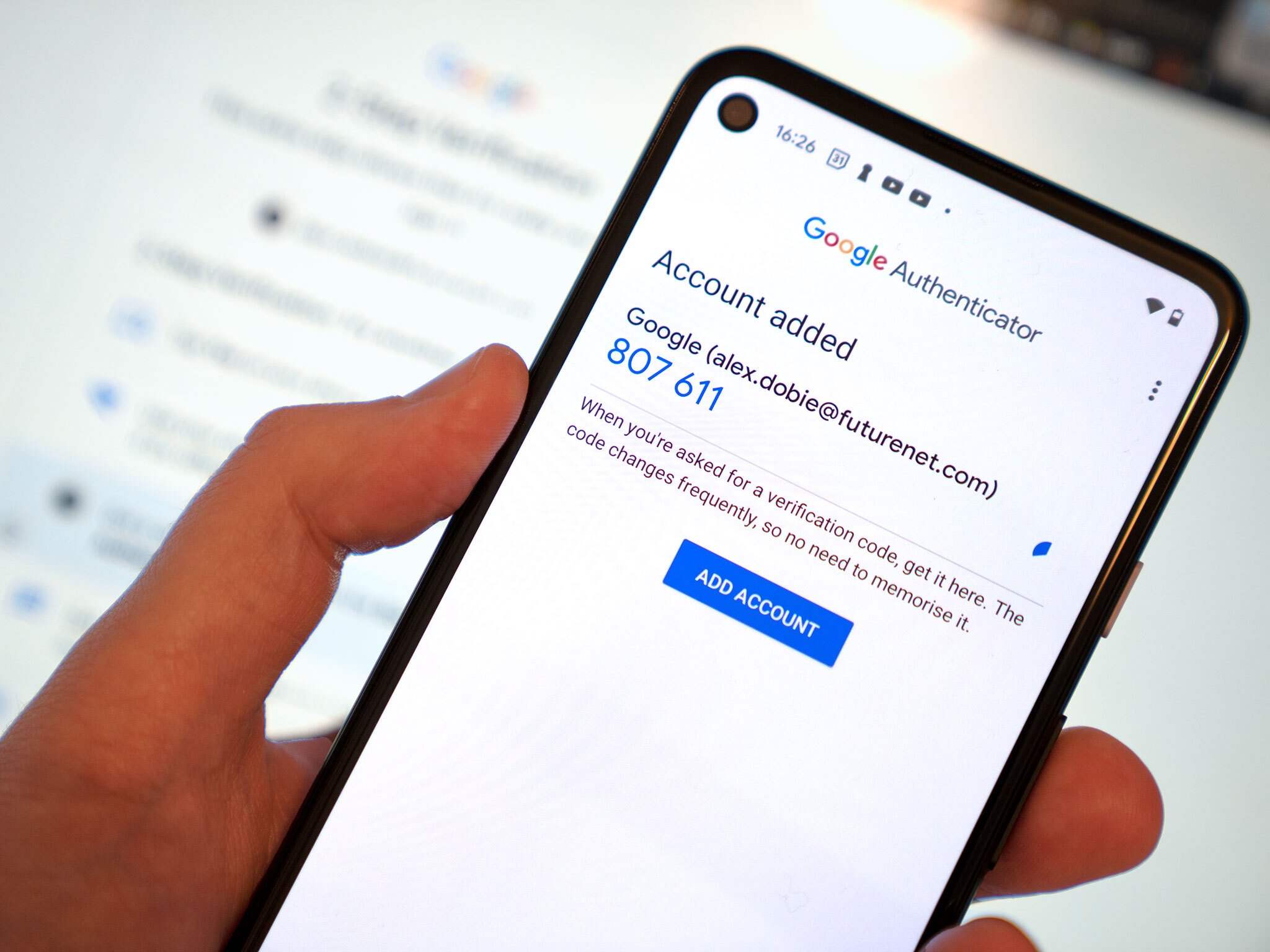
Source: Alex Dobie / Android Central
Authentication apps such as Google Authenticator and Authy are a vast improvement on SMS-based 2FA. They use what's known as Time-Based One Time Passwords. This is a way that an app on your phone can generate complex algorithms without any type of network connection. The same algorithm is used by websites and services to verify that the code is correct. Although authentication apps are more reliable than SMS for 2FA, they aren't foolproof. Although they are offline TOTP-style 2FA doesn't have the same problems as SMS, it does have its limitations. Researchers have found that it is possible to intercept or manipulate data sent by you when you enter the TOTP code on a website. However, it is not simple. Phishing is the real problem. You can create a phishing site that appears and acts exactly like the real thing. It even sends you your credentials, such as your password and the TOTP generated from an authenticator app. This will allow you to log in to the genuine service. It can log in to the real service as well, acting just like you. All the credentials were provided. The downside is that it may not be possible to retrieve the codes you need in case your phone gets lost. Authy, an authenticator app that works across devices, uses a central password to set up everything. Most companies will also provide a backup code set for those times when things go wrong. It makes TOTP less effective, but it offers more convenience for users. It is safe and convenient but not very common. Push-based 2FA
Source: Google
Some services, such as Google and Apple, will send you a prompt when you attempt to log in. The prompt will alert you that someone is trying login to your account. It can also provide an approximate location and ask you to accept or decline the request. You can tap a button to confirm that it is you. Notifications for 2FA are super simple and very convenient. You shouldn't lose your smartphone though. Two ways push-based 2FA can improve on SMS 2FA or TOTP authentication are: You can even make it more convenient by simply reading and tapping a standard notification on the phone. It is also more resistant to phishing, and has proven to be extremely "hack-resistant". But, you never know what the future may bring. Push-based 2FA magnifies the disadvantages of SMS and TOTP: You must be connected to the internet via a data connection (voice and text plans won't work), and you must have the correct device to receive the message. You can expect to use the login prompt on your Google Pixel for other accounts. Push-based 2FA is convenient and secure, despite these two real disadvantages. It will also be considered in Google's future plans for 2FA for your Google Account. It's the winner! However, it is also irritating! 1. 2.
Source: Jerry Hildenbrand/Android Central
It is best to use a separate piece, such as an authenticator device or U2F security keys, to protect any online account. This is also the most convenient and least used. It is set up by using the hardware. To log in from another device, or after a time limit set by an administrator, you will need to use the same device. The device sends a signed code to the server, which is unique to your account and the device. U2F is phish-proof so far. Again, never say never.
A U2F key, while it is not the most convenient and secure method to perform two-factor authentication, is the best. You might not want to use it because it is a pain in the arse.
Although you can set up multiple devices on one account, you will not lose access to your security key. However, you must always have the key with you when you log in to any website or service. To secure my Google accounts, I use a U2F Key. Every 12 hours, I have to give the key to gain access to my Google Enterprise account. This means that I keep a key in my desk drawer, one on my keychain and one in an envelope that a friend keeps in case of emergency. Source: Jerry Hildenbrand/Android Central If you have a key, you can set up 2FA backups. Google will force you to do this. Although this is convenient, it can compromise your account's security as the less secure options are still available for you and anyone else to gain access. Cost is another disadvantage to using a hardware token as a security code. SMS, push-based 2FA or authenticator apps are all free. You will need a security code to use the service. They can be purchased for between $20 and $100. This can be costly as you will need to have at least one backup key in order to use this method. It can be cumbersome to use a security code with your phone. There are keys that can be used via NFC, Bluetooth, or USB. However, no method is perfect. Which method is the best?