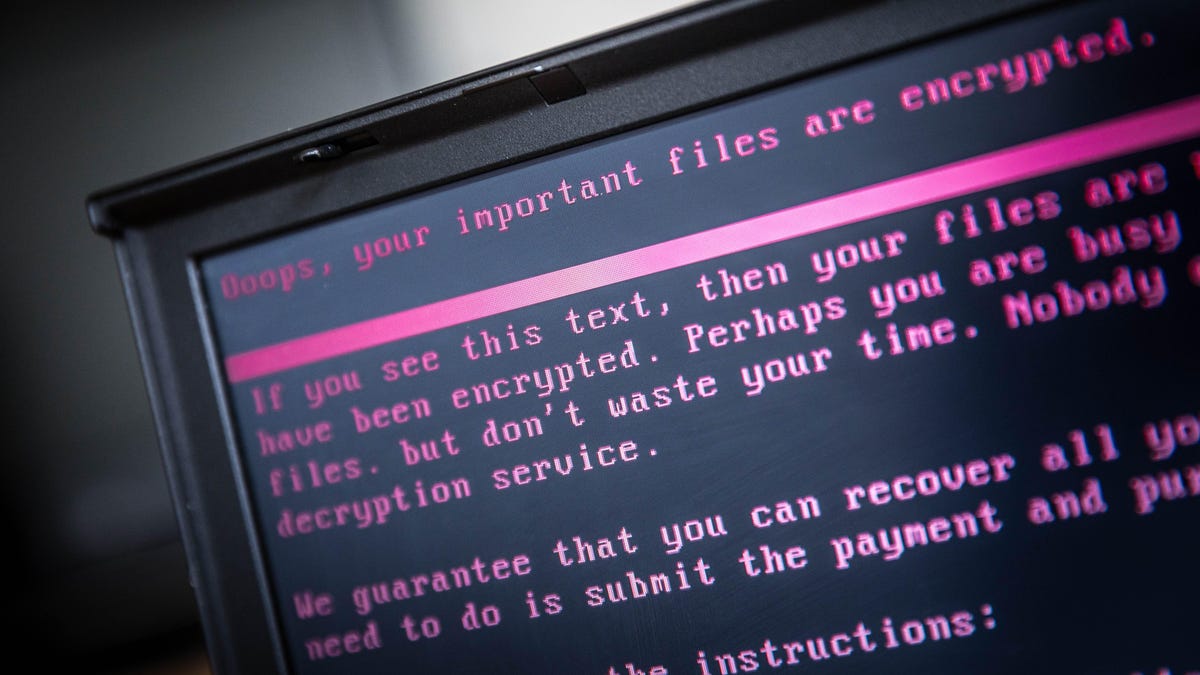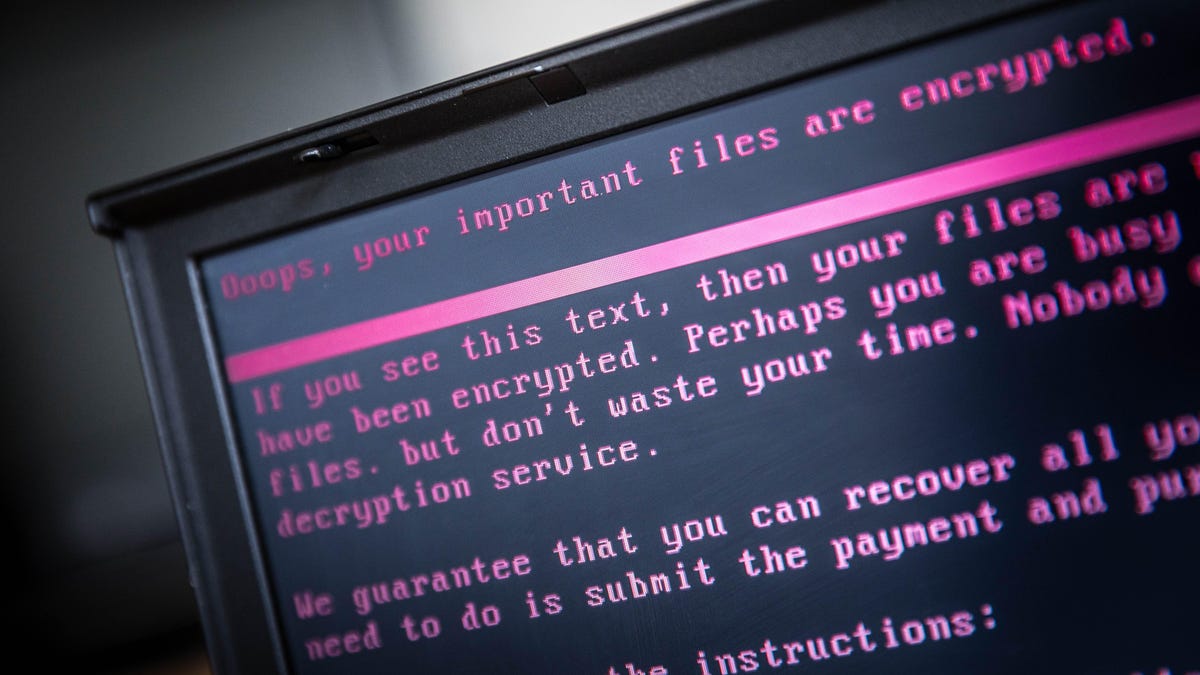
Photo courtesy of ROB ENGELAAR/ANP/AFP ( Getty images )Ransomware attacks on Kaseya, an international IT company, appear to have infected hundreds more smaller businesses that depend on Kaseya's product, many of which are based in the U.S.AdvertisementKaseya revealed Friday that it was the victim of a possible attack. This implied that hackers were targeting VSA on-premises users. VSA should be shut down immediately by customers, according to an alert.Although Kaseya claims that the attack has been limited to a few customers, Kaseya's position within an IT ecosystem could mean that it could have a significant impact on other IT systems making this one of the most successful ransomware attacks ever.Kaseya sells products to managed service providers (MSPs). These companies provide remote IT services to many smaller businesses who don't have the resources or time to do so in-house. Kaseya's VSA cloud platform is used by MSPs to send and manage software updates to clients as well as other issues.The Record reports that ransomware gangs are using VSA to distribute ransomware to companies around the globe. Although it is unclear what caused the attack, or when, security experts report that ransomware is also affecting clients of MSPs who use VSA. The ransomware appears to have infected hundreds more small-sized businesses that depend on MSPs for IT support.Gizmodo was told by Huntress Security that three of its clients were MSPs who use VSA and that as many as 200 other businesses relying on them had been affected.Four MSPs are affecting all clients in the United States and one abroad. John Hammond, senior security researcher at Huntress, stated that MSPs that have thousands of endpoints are being targeted. We have seen evidence that a compromised MSP has spread to all its customers via the VSA.AdvertisementHammond stated that, based on all we have seen, this [is] REvil/Sodinikibi.REvil is a well-known cybercriminal gang which has used ransomware in order to pursue high-profile targets like Apple and Acer. It is also believed that it was the gang responsible for attacking JBS meat supplier, extorting $11 million from the large beef supplier.AdvertisementThe Cybersecurity and Infrastructure Security Agency (USA) announced Friday that it was working to address the ransomware attack on Kaseya VSA and multiple managed service providers that use VSA software.CISA encouraged organizations to read the Kaseya advisory, and to immediately follow their instructions to shut down VSA servers.