Researchers have identified a new type of malicious software that threat actors have been using for the last 15 months to gain access to Microsoft Exchange.
SessionManager is a malicious software that pretends to be a legitimate module for the internet information services. IIS modules can be used to simplify processes on the web. According to researchers from the security firm, 24 organizations have been affected by the SessionManager infections. According to Kaspersky, as of earlier this month, 20 organizations were still infections.
Powerful, persistent, and stealthy backdoors can be deployed with maliciousIIS modules. Once installed, they will respond to specifically crafted HTTP requests sent by the operator instructing the server to collect emails, add further malicious access, or use the compromised server for illegal activities. The requests look unremarkable even though they give the operator complete control.
Pierre Delcher wrote that such modules expect seemingly legitimate but specifically crafted requests from their operators, triggering actions based on the operators hidden instructions if any, then transparently pass the request to the server for it to be processed just like any other request. It's not easy to spot such modules because they don't initiate suspicious communications to external server, receive commands through HTTP requests to a server that is specifically exposed to such processes, and their files are often placed in overlooked locations.
Advertisement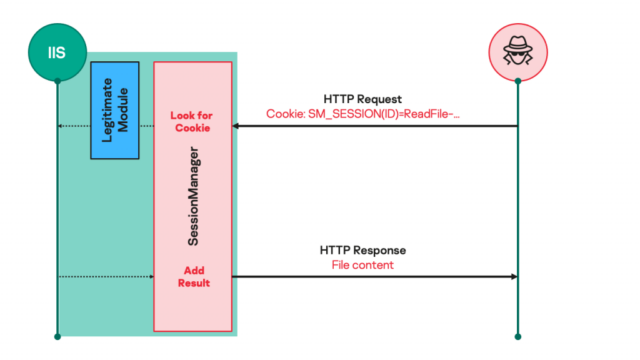
SessionManager can be used to profile the environment further, gather passwords stored in memory, and install additional tools, including a PowerSploit-based reflective loader. At least one variant of the SessionManager was obtained by the company. More features have been added with each new version of the sample. The most recent version of the module has some new features.
Command name (SM_SESSION cookie value)
Command parameters (additional cookies)
Associated capability GETFILE FILEPATH: path of file to be read. FILEPOS1: offset at which to start reading, from file start. FILEPOS2: maximum number of bytes to read.
Read the content of a file on the compromised server and send it to the operator as an HTTP binary file named cool.rar. PUTFILE FILEPATH: path of file to be written. FILEPOS1: offset at which to start writing.
FILEPOS2: offset reference.
FILEMODE: requested file access type.
Write arbitrary content to a file on the compromised server. The data to be written in the specified file is passed within the HTTP request body. DELETEFILE FILEPATH: path of file to be deleted. Delete a file on the compromised server. FILESIZE FILEPATH: path of file to be measured. Get the size (in bytes) of the specified file. CMD None. Run an arbitrary process on the compromised server. The process to run and its arguments are specified in the HTTP request body using the format: t. The standard output and error data from process execution are sent back as plain text to the operator in the HTTP response body. PING None. Check for SessionManager deployment. The “Wokring OK” (sic.) message will be sent to the operator in the HTTP response body. S5CONNECT S5HOST: hostname to connect to (exclusive with S5IP). S5PORT: offset at which to start writing.
S5IP: IP address to connect to if no hostname is given (exclusive with S5HOST).
S5TIMEOUT: maximum delay in seconds to allow for connection.
Connect from compromised host to a specified network endpoint, using a created TCP socket. The integer identifier of the created and connected socket will be returned as the value of the S5ID cookie variable in the HTTP response, and the status of the connection will be reported in the HTTP response body. S5WRITE S5ID: identifier of the socket to write to, as returned by S5CONNECT. Write data to the specified connected socket. The data to be written in the specified socket is passed within the HTTP request body. S5READ S5ID: identifier of the socket to read from, as returned by S5CONNECT. Read data from the specified connected socket. The read data is sent back within the HTTP response body. S5CLOSE S5ID: identifier of the socket to close, as returned by S5CONNECT. Terminate an existing socket connection. The status of the operation is returned as a message within the HTTP response body.
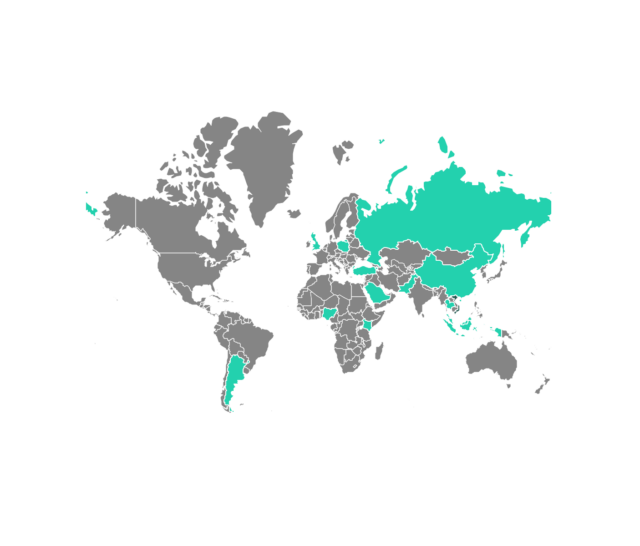
It has medium-to-high confidence that a threat actor called Gelsemium has deployed Session Manager. A deep dive on the group was published by a security firm. The overlap of code used by the two groups is the basis of the attribution.
Disinfecting server that have been hit by SessionManager is a difficult process. There are indicators that organizations can use to determine if they have been exposed to the disease and if they need to take precautions.